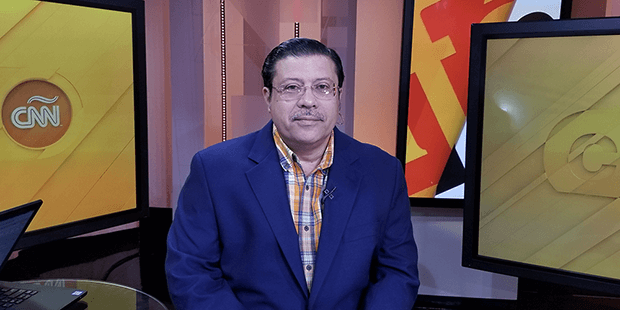
Below is our recent interview with Dr. Luis O. Noguerol, from ADITusa:

Q: Could you provide our readers with a brief introduction to ADITusa?
A: Advanced Division of Informatics & Technology, Inc., (alias ADITusa), is a well-established cybersecurity company headquartered in Miami, Florida, with operations in Silver Spring, Maryland; Washington DC; and Westborough, Massachusetts. The company was opened in the State of Florida in February 2006 and later expanded its operations to three other locations. This is a minority owned and operated business. The owner of this business is Hispanic American.
ADITusa, Inc. began servicing the Miami area small businesses back in 2006 and specialized in cybersecurity and network management; telecommunications; as well as IT training with a differentiator factor from other training companies: all our trainings are 100% hands-on and cover more theoretical content than any other academic institutions in the geographical areas in which we operate.
All our training sessions are equally 100% tailored to our clients’ needs and we never use the approach of “one size fits all.” We developed the ability to explain how to protect your systems and infrastructure, or better, the complete ecosystem, without complicated technical jargon, are always precise, straight to the target, and never failed – not even one time, while performing a Penetration Testing; Data Recovery; and Digital Forensic investigations. The best part, we offer our services at very affordable prices. Of course, this statement is backed up by the multiple reviews we have from past and current customers and can be easily found online.
In the last six years, ADITusa, Inc. has been serving the US Department of Commerce at the Southeast Region and the Department of Defense in different cybersecurity roles and is certified as one of the 11 digital forensic firms with the ability to “talk” in legal cases in the State of Florida.
Q: Dr. Luis, it sounds impressive; let’s start with your background. What were you doing before ADITusa?
A: I have been working on Information Technology and Information Security for over 35 years. To be more specific, the week in which “What’s Love Got to Do with It“ by Tina Turner was making headlines, almost everywhere in the world. I began my professional career on Friday September 7, 1984. I will never forget. I began “punching” cards, later become a Mainframe operator, Programmer – I meant, a Developer; work as a System Analyst, and later a Cybersecurity Analyst. Right before founding ADITusa, Inc., I was the Information Technology Director at one of the most reputable Universities in the State of Florida but let me tell you, those are the good ones… before that…hummm, I don’t even know if I want to talk about this…
Q: Why? Go ahead…
A: Well, I left my country back in 1999…
Q: Where are you originally from?
A: I am from Cuba and I can tell you that the beginnings were very frustrating and discouraging but I realized, very soon, that the only way to achieve my dreams was to continue my education, and I did. By the time I immigrated to USA, I already had an Associate Degree in Mainframes Operation and Programming; a Bachelor Degree in Electronics, and a Master Degree in Mathematics. I have to confess you that reality was very shocking… my first job was working as a janitor in a huge building in Louisville, KY, making almost the minimum salary; I ironed clothes in a dry cleaner; I washed dishes in a restaurant; walk horses in the Churchill Downs – which is the most famous racetrack that annually host the Kentucky Derby; work as a bodyguard in a go-go dancer for almost a year…
Q: No way… are you kidding?
A: Luis is laughing a lot…. No, I am not… for almost a year a lot of bad memories from this place, a lot of dangerous fights, it was complicated but I was living along with my Son, Landy, and I had to do whatever was needed, between quotation marks, to make extra money and provide him with the basics… it was really a very challenging time but things happen…. you know… all of this serves as an inspiration to launch ADITusa… I also worked as a High School Teacher, taught Math, becomes a store manager at AutoZone; I don’t even know what else I did, probably I forgot something on my list…, I was a Part-Time Judo Instructor for almost two years…
Q: No way… are you kidding?
A: Luis is laughing a lot…. No, I am not… I am not… I am a Black Belt Second Dan and was recently promoted to Sensei, but is better if we don’t talk about this because I’ll deviate from the conversation… Judo is in my blood, a very important part of my life… later I began working on IT and Cybersecurity again… good memories… thanks for asking those questions but is better if I can get back on track to the interview questions… I think that education was the key for me to open ADITusa, also, a substantial part of my life… I understood the needs back in 2006 when I decided to open the company and more importantly, I recognized the lack of expertise in Cybersecurity in the private sector, I just took the chance, and here we are today…
Cybersecurity is the only topic that I can talk about it for 24 hours straight, without drinking water, stopping, or resting, this is my major motivation in life, apart from my family and friends… they go before.
Q: When we were doing our research, we find out that you also hold a Doctoral Degree in Information Technology and own multiple IT certifications… how you can do all those things simultaneously?
A: Luis is laughing again…. Well… I have been asked this question probably hundred times and the reality is that I always have time for everything, but specially, to improve my professional skills, I’m very handy in cybersecurity, not a typical person that repeat things or Google solutions… I do everything by myself… it takes a lot of time but I enjoy the journey…. Here is the problem. I’m very often invited to speak and present in international cybersecurity conferences and summits and I cannot fail in front of the audience…. I simple can’t do it and for that, I must master the topics, it takes a lot of time, years, but is doable… and I encourage everyone to step-in and do anything they can to become better professionals, in whatever they do, but you want to be among the best in the world… this is easy to say and to achieve if you are focus, if you believe in yourself, otherwise, you will be just another one, between quotation marks, and honestly, I don’t like this title…
Q: But you never told me about your Doctoral degree when we spoke…
A: Ah, OK… I’m going to be very sincere… for me, it was really demanding, complex, and at a point, I was ready to quit. Thanks to my Son – Landy; and my adorable wife – Moraima, I didn’t, and now I’m happy for that… it took me almost seven years to complete my Doctoral degree. I did it at the University of Phoenix, and I’m proud of what I have achieved. I graduated cum laude in Information Systems and Technology… what a pain… but a reality now.
In my case, it has been extremely helpful… and I know that it doesn’t work equally for some graduated, but as I said, in my case, very convenient. All depends of your dedication… I’m always thirsty to know more, I can’t stop and don’t know why, but I can’t…, and I also thanks all my family and friends for their unconditional support as well…my parents – I would do anything to make them happy….
Q: How about the certs?
A: Ohhh, OK, I forgot that part… actually, I’m a holder of 79 IT Certifications…
Q: Wow, really impressive!!!
A: 57 of those are in cybersecurity … and this is something I have been doing not only for me, but for ADITusa. It is of extreme importance today. Organizations looking for help in cybersecurity, requires many times, a set of artifacts as part of the compliance and regulatory process and here is where certifications help. A win-to-win situation…
Q: While doing our research, we find out that Covington Who’s Who selected you as an Honored Member of the Executive and Professional Registry, back in 2014, and in 2016, you were the C|CISO of the year, worldwide. This is big…, could you please tell me about this?
A: It was a real privilege. Actually, one of the main reasons for the nomination was a recognition by the American Institute of Physics for my contribution to prove a fault in the Snell’s Law; and in addition, I was recognized for developing and proposing a brand new mathematical model that combines the logic of the Elliptic Curve and Lagrange’s theorem with a PIN Block encryption scheme to minimize risks associated with electronic data leakage when using Multimedia Messaging Services (MMS).
Another factor was that I was able to reduce the electronic fraud by 39% for two of the major financial institutions in Central America in less than two years. It was really amazing. I was ranked number 17 by the Business Leaders Magazine in 2012 as one of the most influential IT leaders in the USA East region. All of these, have been contributing to the success of ADITusa.
In regards to the C|CISO, I was selected by the EC-Council Foundation and the InfoSec Institute among 2143 candidates from 121 countries. I still cannot believe it myself, but this is a fact… (Luis is laughing). The Cybersecurity Excellence Awards is an annual worldwide competition honoring individuals and companies that demonstrate excellence, innovation and leadership in information security. I’m proud and indebted to the panel that vote for me, I’ll never forget.
Q: One more question about you, before we talk about ADITusa. What happened in 2012?
A: In 2012? I don’t remember, what do you mean?
something about Hacking we read….
Ohhh… Luis is laughing again; this year I was the winner of the “Hacker Halted” Hacking competition. It was almost the beginning of what is now a huge event. In 2012, the competition was here in Miami, at the Intercontinental Hotel and I was able to hack a recently released Windows Server 2012 Operating System, in 33 minutes – to be more exact. It was really nice and grasp a lot of attention at this point. I was competing by myself vs. three teams from different countries, Israel was second and it was really remarkable… I just found a glitch in the operating system that I was able to exploit in the way the credentials are stored in Active Directory and you know what? They have a similar problem seven years later; I can’t believe it…
Q: OK, now talking about ADITusa, what types of services do you provide to your clients?
A: OK, here we go. We specialized in Penetration Testing, also known as PenTest; Data Recovery; Digital Forensics, and Technical Training.
Our slogan is: “You concentrate on your business, and we take care with the security of your electronic data.” We master what we do because we have been doing it for more than 35 years. We have been winning the trust of our clients by doing and probing, NOT by avoidance or saying. PenTest is usually a set of different examinations used to corroborate the security of the company’s electronic data, discover hidden threats in addition to discontinue the leakage of electronic data. We document every step, without exceptions, and suggest actions to minimize existing vulnerabilities and improve our customers’ cybersecurity posture. This information is provided to the clients in an extremely well detailed report, including graphics, screenshots, explanations, and in the majority of the cases, a real lifetime video showing how the system (s) was/were compromised. All tools used are included in the report as well and the rationale behind.
At ADITusa, we aggressively try to abuse existing weaknesses at the system, network, or local level. It means that we scan your entire ecosystems and identified existing and exploitable vulnerabilities, including telecommunication systems and mobile technologies. We do “White Box” Testing, in which the client provides us with some relevant information about the network topology and/or infrastructure before the beginning of the testing examinations as for example login information (user names, passwords, tokens). This type of tests requires less time and is much simpler, but usually demands the interaction from the subject of the test. We do “Gray Box” as well. In this case the client provides us with some basic information as for example company’s URLs exposed to the public; and “Black Box” testing in which we need to find out everything in our own. I personally love this approach but of course, is more time demanding.
When it comes to Data Recovery, we are one of the very few companies that have been successfully proven through years what we can do. We follow our promise and always speak clear from the beginning, without using a super sophisticated technical jargon and this is not something clients are going to find in the majority of the companies that offer similar services.
In real life situations, the statistics show that recovering electronic data is a daunting task that would cost millions of dollars to the data’ owners. Due to the complexities related to data loss prevention, it is very hard to precisely enumerate all the reasons why data can be corrupted or deleted. It could be due to negligence, wrong decisions, lack of knowledge, accidents, electrical failures, physical or mechanical damages, computer malware, etc. The problem is that when the electronic data is deleted, for whatever reason, the possibilities of recovering such data becomes a very complex task, especially when time has progressed from the moment of the deletion.
At ADITusa, our inventory includes the most advanced tools for Data Recovery available in the market, categorically speaking, we have what is needed, and we keep updating it as new technologies become available. Under no condition what¬so¬ever, will we share with anyone any type of information related to the services we provide for our customers. A wise man once said “business is between those who do it”. To guarantee what we claim in terms of privacy, we will extend a confidentiality agreement in writing, before we begin the process. We take the privacy of our customers very seriously.
Our portfolio for Data Recovery includes the following devices and technologies:
- Recovery of data after the logical destruction of the file system (FAT12, 16, 32, exFAT, NTFS; NTFS5; and ReFS)
- Recovery of corrupted data from any type of storage devices like USB Flash Drives, PenDrive, SIM Cards, miniSD, and most of the CDs/DVDs – this last one is not an easy task, by the way).
- Recovery of data after the storage devices or Hard Drive has been formatted and Yes, I said, after the storage have been formatted.
- Recovery of Data after a re¬installation of the Operating System.
- Recovery of Data from any type of Hard Drive, (IDE, ATA, SATA, SCSI, SSD). Recovery of Pictures, Videos and documents, are guaranteed. Those are usually the easy ones.
Our success has been possible thanks to 34 clients in the last 13 years, which have allowed us to recover an accumulative data content of more than 123 TB successfully.
What makes our services unique is not only our extensive experience of more than 35 years, but also the professional standards we follow when conducting business, our highly skilled staff, and the guarantee that if your device still operational, we will recover your valuable, priceless data no matter the effort it takes. In many cases, we can recover the data from physically damaged devices as well, but this is a different conversation. The only thing we cannot guarantee is a specific time and this statement is an example that in ADITusa we always speak clear from the beginning. Let me said that, if any other vendors or competitors mentions that to you, I meant, a specific time, they are most likely scamming you, or taking advantage of your lack of knowledge regarding the subject of the matter in the topic and field.
Data Recovery is not about time, it is about experience in the first place, deep technical knowledge, resources, and having the needed tools to perform the task. Sometimes, data could be recovered in terms of hours, while at other times, it could possibly take a certain amount of days, however, we do our best to perform the diagnostic in the first 3 working days, and usually complete the recovery between 3 – 7 working days. As mentioned at the beginning we tailored all our solutions, without exceptions.
The other strong solution we provide at ADITusa is Digital Forensics. With the growing popularity of different types of electronic devices, the necessity to have certain control of the electronic data is not only a legal requirement, but also an ethical obligation. The question is: how do you know you are protecting your electronic data? As time passes, judicial systems all around the world are accepting more electronic evidence instead of traditional ways as for example, papers. This is an ongoing process with important changes from State to State and from Court to Court. At ADITusa, we know, very well, the existing regulations State by State, and believe me, this is easy to say but no know.
The question to ask yourself is: what I can do to discover whatever happened in my system with exactitude, to prove that somebody has been acting inappropriately or how and who put my company’s information at risk? Digital Forensics deals with the assessment of electronic assets, (including but not limited to any type of storage devices), to seize, investigate, analyze, and determine what has been happening in your information technology systems; including mobile devices, mainly when you have some suspicions about the occurrence of any type of abuse, crime, (fraud), or just a simple intrusion in your systems.
Due to the innumerable different types of branch technologies, the characteristics of each one, and the complexities related to the protection of electronic data, the field of Digital Forensics has been gaining importance and its role in the modern enterprise is simply unavoidable.
At ADITusa, we will provide our clients with the specific evidences, (never-ever general artifacts), they need to prove any type of “wrong doings” or attacks towards their organizations, and possibly to substantiate the act of corporate espionage within the company. Interpreting electronic data in raw format requires an extensive theoretical preparation, (please note that I said theoretical preparation, intentionally), and proven skills, especially in the fields of electronics, physics, mathematics, and information technology. At ADITusa, we are experts on all of these fields as well. This is what we do. Personally speaking, I’m one of the 11 Digital Forensic Experts accredited by the court system to testify in legal cases in the State of Florida.
As mentioned at the beginning, ADITusa have been a leading organization providing IT and Cybersecurity Training to the private and public sector, including the Department of Defense. All those trainings are 100% hands-on, without exceptions. In the last five years, we have been delivering 19 training sessions to the day, January 2020, in a bootcamp format, at different military bases including the Edwards Air Force Base, in the Antelope Valley, California and Hickam Air Force Base in Hawaii, among others. After 35 years in cybersecurity, I know exactly what skills are needed to minimize cybersecurity issues. This is where my 79 IT Certifications and well prolonged experience in the field of electronic data security counts. When it comes to cybersecurity or IT training, I do not delegate in any members of my team. I do this, myself.
Q: How has cybersecurity industry changed over the past few years?
A: This is a good common question I got when presenting at international conferences. I can assure you after 35 years of actively working in the field, that any sounded/fancy, (between quotation marks), response is going to be out of the target. The amount of dissimilar technologies available today, including telecommunication equipment – with their particular specifications, are simple incomparable to what we have for example back in 1984, when I began my professional career. From modern Satellites Systems to the G5 technology for wireless communications… everything has been changing so fast, that when I look, retrospectively, I can’t believe it myself. Current bandwidths and storage capacities is something unimaginable 35 years ago. Remember, when I began, we were using sequential access tapes, drum disks; 8, 5.25, and 3.25 inches’ floppy disks, punched cards, monochromatic monitors…, very different technologies…
Cybersecurity has been changing, radically speaking, drastically, really! The amount of data we handle before probably in a five years’ period is handled today in a matter of minutes. There is no a comparison point in cybersecurity before and now – of course problems 35 years ago were different as well, simple like that but more importantly, we are now technology’s dependents, for almost anything. It doesn’t happen 35 or even 25 years ago. The scenario is completely different and consequently, experience is a key in cybersecurity. “Script kiddies” and “googlers,” I meant, regular users of Google or any other type of search engines, represent one of the biggest concerns nowadays. Effective cybersecurity cannot be solved by any of those two categories of people. Cybersecurity is bigger than this…, much more!
 Recommended: Baicells Technologies Delivers Innovative Cloud-Based 4G/5G Wireless Solutions
Recommended: Baicells Technologies Delivers Innovative Cloud-Based 4G/5G Wireless Solutions
Q: What makes ADITusa unique? How do you stand out from your competition?
A: First and foremost, we are unique because we have been in the field, actively working for the last 35 years, straight in the road. No wording or trying to play smart as many other companies in the market in which the message is intended to confuse the audience and prospective clients. Every time you heard, for example, “X amount of years of combined experience…,” I recommend you run away. When I founded the company 13 years ago, one of the pillars was my personal experience in the field. Today, after 35 years of active and sustained service in Information Technology and more specifically, in cybersecurity, I can say that we do not have too many competitors in what we do and I completely understand that it might sound very arrogant but this is the raw reality, it is.
The reason why we have been earning the trust and respect from our customers, including the US Federal Government and some of the major financial institutions in Central and South America, is very simple: we deliver our promises when it comes to cybersecurity. Period. Listen, I do not consider myself a sales person at all, actually, I always joke about this with my Son. Instead of what probably a marketing or sales person would recommend, I always said to our customers, and prospective clients, call others before you call us (contrary to the pledge of the great majority of the companies), and compare what they claim to do versus what we offer. The final decision is yours, but keep in mind that putting the security of your electronic data in inexpert hands, is not a savvy decision, at all.
At ADITusa, we secure our clients’ systems, including applications, networks, and websites. We perform full vulnerability assessments, baselines analysis followed by a full and detailed report that include remediation steps for all findings, without exceptions; we always include in our reports all kinds of artifacts as screenshots, descriptions, flow charts, and even videos captured in real time, showing the process from the beginning to the end. In other words, we document all and every single steps and findings, and in addition, we do not release any information about your company, neither about our partnership, very rare, right?
We respect our customers as we do our self. We take care of them as we do for us. We work tirelessly to protect their electronic data as we preserve the image, reputation, and integrity of ADITusa. I’m very tactful and never put money over our pledge, “you concentrate on your business, and we take care with the security of your electronic data.”
Q: What are the company’s plans and goals for the future?
A: Simple. Surpasses our customers’ expectations. Keep our arsenal of tools current. Provide similar services to our customers, with the same kind of quality we have been providing. We plan to continue in the customers’ minds and we can always be contacted at:
Activate Social Media:


 Recommended:
Recommended: