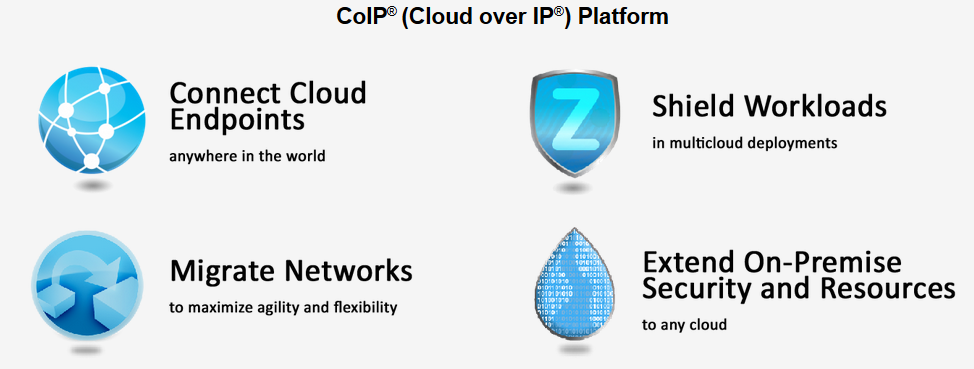
Zentera Systems provides the CoIP, “Cloud over IP” platform that enables companies to protect their production workloads from on-premise datacenters to public, private and hybrid clouds. Earlier this month company launched a new CoIP platform feature – the industry’s first true cloud security overlay solution that brings third-party security capabilities to the cloud. Below is our recent interview with the Director of Products at Zentera Systems, Rabiul Hasan:

Q: Could you provide our readers with a brief introduction to Zentera Systems?
A: Zentera Systems is a networking and security company focused on the multicloud. We provide the CoIP® platform that enables companies to protect their production workloads from on-premise datacenters to public, private and hybrid clouds—the multicloud. CoIP stands for “Cloud over IP” and is available to organizations through our partners.
CoIP directly addresses the security threats that are specific to the cloud and multicloud world. One such threat is the new attack surface that is exposed when utilizing public cloud datacenters – east-west threats, or threats that are intra-domain within a single cloud, datacenter or environment. When companies go to the cloud, one big concern is about their unknown neighbors. Another multicloud threat is called north-south threats, or threats between domains – inter-domain threats. Many enterprises build permanent networks that connect cloud workloads back to their on-premise environments. When an attack and compromise happens in the remote cloud workload, hackers can use those connections to come back into the enterprise. Essentially, enterprises risk leaving a door open for intruders to come in. CoIP closes that door.
 Recommended: ViriCiti Raises Funds To Expand Its Cloud-based Telematic Service Across The US
Recommended: ViriCiti Raises Funds To Expand Its Cloud-based Telematic Service Across The US
Q: You’ve recently launched the industry’s first cloud security overlay solution that delivers third-party security capabilities to the cloud; tell us something more?
A: Earlier this month we launched a new CoIP platform feature – the industry’s first true cloud security overlay solution that brings third-party security capabilities to the cloud. Integration partners can now offer their industry-leading security features throughout the multicloud to their customers.
CoIP itself is a virtual infrastructure that helps companies isolate and shield their application workloads in the cloud. The workloads are effectively invisible on the internet to malicious users or hackers, as well as to cloud provider operations. CoIP provides the highest level of cloud security assurance to enterprises and allows them to keep their security, physical network, and compliance measures intact during and after cloud workload migration.
Q: Could you explain the function and advantages of Zentera’s CoIP solution?
A: In contrast to conventional edge-to-edge solutions like VPNs, CoIP is an endpoint-to-endpoint solution, which allows security to operate at both the network and the application layers. Furthermore, the endpoints can be set to individually allow only specified applications to use the network. And the network itself is not permanent. Instead, it is on-demand and event-driven, which increases security by reducing the attack surface in the cloud. CoIP security features include network encryption to protect traffic and data; microsegmentation to protect against east-west threats, and application interlock and whitelisting to protect against north-south and east-west threats.
CoIP is a single platform that offers the required functions and is automated. There is no need to modify existing IT technology. With CoIP, enterprises can migrate production workloads to any cloud with significant productivity gains. The next-generation enterprise multicloud infrastructure, using CoIP, will be completely overlaid, with no “rip and replace” of legacy infrastructure.
I’d like to highlight our recently-announced support for CoIP integration with security engines. This illustrates how CoIP can give organizations flexibility and provides them with defense-in-depth capabilities in the cloud that they have on-premise by using their existing enterprise security services. Our integration partners can now offer their industry-leading security features throughout the multicloud to their customers. As a result, security companies can become the end-to-end security vendor of choice and can offer new cloud security services to attract new customers.
Overall, CoIP brings great efficiencies to businesses in multiple ways. They can migrate, protect, and run multiple production workloads in the cloud with ease, giving them flexible business scalability with partners and customers. CoIP’s on-demand networking and cloud services means that businesses pay for extra resources only when they are being used. And since CoIP does not require changes to the existing infrastructure, there is no need to wait for approval from security and legal teams before CoIP can be used to benefit the business.
 Recommended: Pioneer Of Internet Technologies, Visicom Media Helps Organizations Monetize And Drive Traffic On The Web
Recommended: Pioneer Of Internet Technologies, Visicom Media Helps Organizations Monetize And Drive Traffic On The Web
Q: What are your plans for the next year?
A: In the first half of next year, there will be industry-leading security, telecom and cloud service providers offering CoIP capabilities as part of their service offerings. We also expect that 2017 will be the year that infrastructure-independent networking, as it’s starting to be called, will be recognized as a critical element in multicloud deployments, which should accelerate the growing interest in solutions such as ours. We can help multicloud become the “new normal”.
 Recommended: Website Optimization Platform Reactful Plans To Accelerate Product Development
Recommended: Website Optimization Platform Reactful Plans To Accelerate Product Development
Q: Who is your ideal customer and why?
A: Enterprises today are moving production workloads to the cloud and are inevitably using multiple clouds. This will lead to an increasing demand for cloud provider interoperability, that is, to be cloud agnostic.
CoIP serves a wide range of customers and use cases. Our ideal customer is an enterprise wanting to migrate one or more applications over to the cloud while preserving their existing security and compliance measures. Or it might be an organization which already has applications in cloud environments. Popular use cases include extending sign-on capabilities across datacenters, consolidating datacenters, and connecting datacenters internally.
Activate Social Media: