Below is our recent interview with Netanel Davidi, CEO & Co-founder of Vdoo:

Q: For those who have never heard of it, how would you describe Vdoo?
A: We founded Vdoo in late 2017 after identifying a crucial need in the market for securing connected products and embedded systems. In the past few years, a staggering number of devices (~25B to date) across many industries (industrial, consumer, medical, automotive, etc.) have become connected to open and local networks. This has led to a significant increase in cyberattacks on connected devices and products, often with devastating consequences for large corporations and individuals. We assembled a team of top-notch experts with years of experience in embedded software architecture and vulnerability research, reverse engineering, and code analysis to come together to create Vdoo. Now, three years later, we have grown to a team of almost 100 employees, with offices around the world – Tel Aviv, Japan, U.S., and Europe.
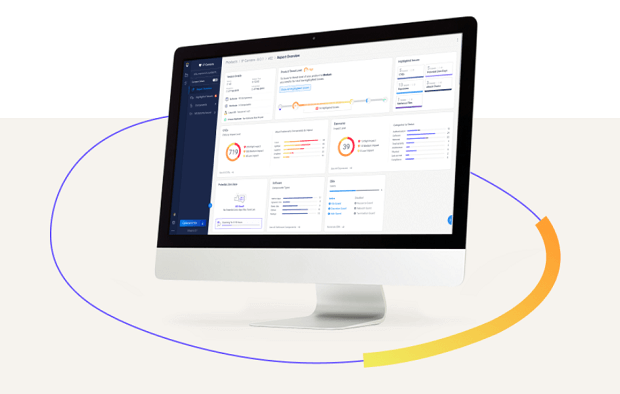
Vdoo provides organizations with a single platform that automates software security tasks throughout the product lifecycle and enables device creators and users to focus on the risks that matter most. Our approach looks at the connected product in its full context, just the way adversaries do. Automating advanced security research techniques for the entire product’s software stack results with better accuracy and uncovering blind spots that cannot be identified via traditional source code analysis or manual effort. The Vdoo platform reveals, prioritizes, and mitigates first- and third-party software security issues and configuration security issues by analyzing each product’s software security posture. We are helping organizations deal with a wide range of security issues that put their software products, services, and customers at risk, including flawed security design, configuration risks, hardening issues, potential zero-days, CVEs, and other security requirements to meet standards and regulations. We are unique in our ability to produce highly accurate results, prioritize and solve them without requiring access to the device’s source code, and save organizations considerable time, effort, and friction in dealing with false-positive security issues.
 Recommended: FourQ Offers Solution For Automating Intercompany Billing And Invoice Management For Multinational Organizations
Recommended: FourQ Offers Solution For Automating Intercompany Billing And Invoice Management For Multinational Organizations
Q: Who are your clients and what are some of the key challenges you’re helping them solve?
A: Our customers are among the world’s top device manufacturers and deployers and span across every industry, geography, and type of connected product, such as automotive, industrial, medical, smart buildings, telcos, and utilities. We provide product security teams, Dev teams, DevSecOps, and compliance officers in these organizations proactive vulnerability discovery, mitigation, standard compliance validation, and real-time protection and monitoring across the entire product lifecycle from development to post-deployment.
We enable our clients to scale their product security capabilities across multiple business lines. Our platform smoothly integrates into standard development processes, allowing enterprises to launch the most secure products with shorter release cycles and less effort from dev and security teams and enabling them to focus exclusively on actual risks.
Q: How would you convince the reader to start using Vdoo solutions?
A: The threat landscape for connected products has become complicated and multi-dimensional. Adversaries come in many shapes, and regulation is tightening. At stake are business continuity, brand reputation, revenue, consumer data, and sometimes even physical harm. With so much on the line, stakeholders must ensure they are at the forefront of product security. Furthermore, consumers and organizations grasp superior security as a competitive advantage, a sign of quality and a business opportunity. This is what you get with Vdoo.
We offer comprehensive coverage and benefits beyond traditional AST tools and manual efforts in a single automated platform. We enable enterprises to launch the most secure products, both new and existing, with shorter release cycles and less effort from dev and security teams. This saves time and overhead on the manual review of false-positive alerts, as well as money and effort on debugging and fixing code. Vdoo offers you the most advanced product security while reducing operational costs and facilitating standard compliance.
Q: You’ve recently raised $25,000,000 in Series B funding; can you tell us something more?
A: In this round, Qumra Capital and Verizon Ventures joined existing investors (83North, GGV Capital, WRVI Capital, Dell Technology Capital, NTT DOCOMO, and MS&AD Ventures). The new funding and strategic investors will allow us to expand our range of solutions for device deployers such as telecommunications companies and utilities. Over the last year, especially throughout the pandemic and the shift to working from home, we have seen a huge market demand from companies that are deploying devices such as routers, connected home appliances, and smart meters. Now, we are expanding our offering so that device deployers can quickly and easily vet the security and standard compliances of the devices they are deploying to end-users’ homes and continue to monitor and protect their devices over the lifecycle of the product.
Q: What are your plans and goals for the future?
A: The world’s top manufacturers and deployers choose to work with Vdoo because they recognize the importance of securing their products. We have big aspirations, and we want to bring automated, out-of-the-box product security to every organization that wants to be confident its software is secure. We want to create an ecosystem where manufacturers, deployers, certifications bodies, regulators, and vendors all work together to make more secure software for all of us as individuals.
Last Updated on February 27, 2021
Activate Social Media:


 Recommended:
Recommended: